Last week my mother-in-law’s gmail account got hacked. It’s still not clear how the hackers got access to her account, but it is a great case study to look at how to be prepared and what to do when it happens.
Skip the story, go straight to lessons learned or what to do if you’ve been hacked.
First off, the Story
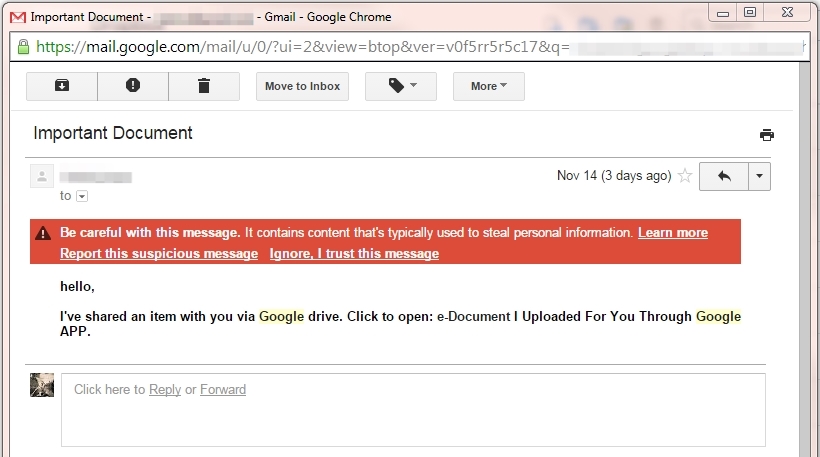
On Friday morning, we all received an email from Louise (not her real name) that read as follows:
[blockquote]hello,
I’ve shared an item with you via Google drive. Click to open: e-Document I Uploaded For You Through Google APP.[/blockquote]
It was pretty clearly a scam, and some of us using gmail even had big red alerts about the suspicious nature of the message.
What to do next wasn’t so clear.
Since the hackers had access to Louise’s gmail account, replying by email to let her know she’d been hacked wasn’t necessarily going to help. My own mother, for instance, replied to ask if it was legitimate, and received a response telling her it was safe, and to go open the link. Obviously, the hackers were watching
Moreover, Louise is currently travelling in New Zealand. When I received the email at 10:00 in the morning, it was the middle of the night there, so we had no way to contact her. Without her password, there was nothing we could do to stop the spam or alert her contacts until she woke up.
We eventually got the password, but when I logged into her account, I didn’t see anything suspicious. No alerts from Google, no outgoing messages, no responses from concerned friends and family. I checked to see whether they’d changed her reply-to address (as hackers had done to a friend of mine last summer), but that was also normal.
After some more investigation, we discovered the following.
What was happening
After gaining access to Louise’s account, the hackers had done a few things.
First, they’d enabled POP access, allowing them to download her messages to a 3rd party client (like Outlook or Sparrow), and send messages through that client without gmail storing them. This way, we couldn’t see what they had sent, or to whom.
They’d also created filters to delete all incoming messages. They could download them using POP access, but we couldn’t see any received messages. Because of this, informing her by email about the hack wouldn’t have helped.
A curious question
One thing they didn’t do, though, was change her password. I found this strange, until I checked the Recent Activity under Account Settings > Security. There I noticed that someone had “Passed a sign-in challenge” in Subang Jaya, Malaysia, earlier that morning. Google doesn’t provide any documentation about what that means, but our working theory is that the hackers somehow accessed her account without actually knowing her password, and without which they weren’t able to change it.
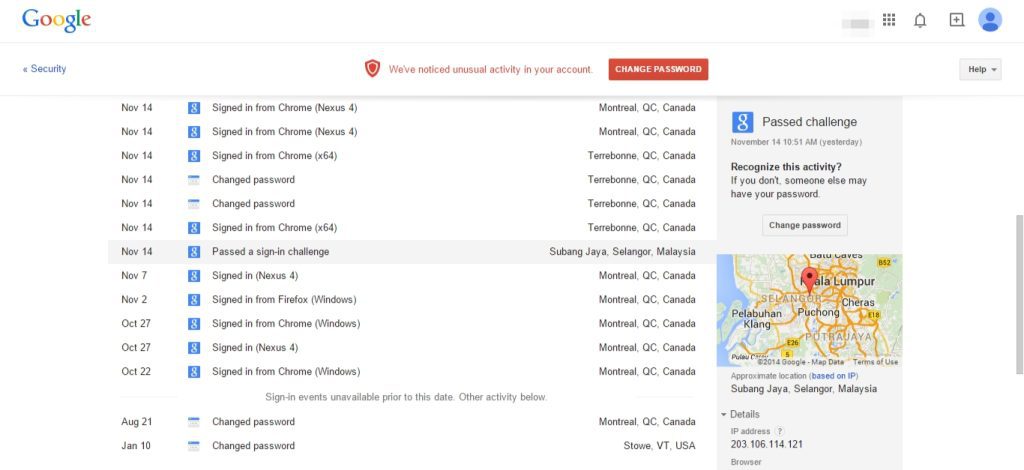
Even stranger, Google didn’t send an alert about this very suspicious activity. My wife is set to receive any security alerts from her mother’s account, and later that day we received two alerts about attempted logins from New Zeland, so it’s surprising – and disconcerting – that we didn’t receive alerts about the sign-in challenge.
Lessons learned
After all is said and done, we’ve learned the following lessons, which you should take to heart.
Be prepared
1. Secure your accounts
All your passwords should be unique and complex, though complex doesn’t necessarily mean difficult to remember. We’ve previously posted guidelines for creating a secure password she’ll actually remember, as well as a run-down of password managers and two-factor authentication.
2. Give your passwords to someone you trust
As I mentioned, once your account gets hacked, how are people going to let you know? Sending an email to your hacked account may not help, and you may not be able to respond quickly.
Give your important passwords to someone you trust who is savvy enough to know how to respond to just such a situation. Send them a link to this article, as well, so they know the procedure to follow if something goes wrong.
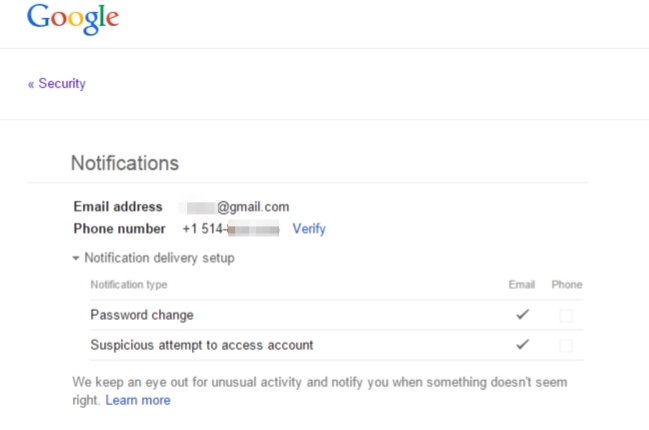
3. Get alerts on your phone
Most modern email services like Gmail and Outlook offer the ability to receive security alters on your phone. This is helpful for getting timely alerts that are more difficult for hackers to disrupt.
In Gmail, go to Accounts > Security > Send phone alerts. On Outlook.com (formerly Hotmail, from Microsoft, go to Account > Security & Privacy.
4. Use a completely separate – and secure – password recovery email address
Gmail and Microsoft both require you to use a separate email address for password recovery. Usually we use a work address, or an alternate free address. But this still relies on your availability. Why not use a trusted friend or family member for password resets?
If you ever actually need to reset your password, you know where to find them. And security alerts will be sent both to your account and the alternate account, so they’ll be alerted to password changes, suspicious login attempts, and other problems even if you’re not available.
5. Regularly review the apps that have access to your account
We’re no longer the only ones with access to our accounts. Lots of smartphone apps, websites, and services use secure tokens to get information about you, and we often want them to have that access. But over time, we enable that access for lots of services that we then stop using or forget about. And the more third parties have access – even secure access – the more vulnerable we are.
It’s worth checking every so often who has access to our accounts, and clearing out old apps you don’t use anymore or recognize.
What to do if you’ve been hacked
Here’s a quick run-down of how to react if you or someone you know has been hacked
1. Change your password
Change it immediately. Change it twice (why not). Change it from a different computer, in case your computer’s been compromised.
And if it’s a friend changing your password for you, make sure they don’t send it to you by email.
You should also consider using a password manager or turning on 2-factor authentication.
2. Check your reply-to address
The hackers may have changed your default reply-to address, so even though people may think they’re responding to you, they’re actually sending emails directly to the hackers.
3. Check if POP or IMAP access is enabled
If you’re not using POP or IMAP access (or if you don’t know what that means), it shouldn’t be enabled. Make sure it’s off.
If you are using POP or IMAP access for a third-party client, consider disabling it at least for a few days.
4. Check if the hackers have enabled email forwarding
Most email providers offer a feature to forward all your email to a different address, useful if you have multiple email accounts that you check in a single place. But hackers can use this feature to get copies of all your incoming email.
Google and Microsoft both show you alerts every time you log in if email forwarding is enabled, but not always. Check your forwarding settings, and make sure you recognize any addresses there.
5. Look through your mail rules
Google calls these filters, but whatever they’re called, they can be used to delete incoming messages, forward messages, and do lots of other often-useful but sometimes-nefarious things.
Look carefully through your email rules to be certain they all make sense.
6. Watch for suspicious sign-ins and login activity
After a hacking incident, it’s important to watch for suspicious activity. Use your mail provider’s security settings to monitor recent log-ins, password resets, and more.
Links
For more guidance on what to do after a hacking incident or if you’ve been locked out of your account, you can see Google’s Compromised Gmail Account article, and Microsoft’s “My account has been hacked” article.